CBS News Live
CBS News New York: Local News, Weather & More
Watch CBS News

The controversial plan charges a fee to enter Manhattan's Central Business District.

The complaint alleges the students have been victims of anti-Palestinian discrimination and harassment.

Harvey Weinstein's 2020 conviction on felony sex crime charges has been overturned by the State of New York Court of Appeals.

Former National Enquirer boss David Pecker appeared on the stand for the third day, detailing an agreement the tabloid made with a former Playboy model.

The New York Giants selected wide receiver Malik Nabers with the 6th overall pick in the 2024 NFL draft.

The New York Giants have six picks in the 2024 NFL Draft, which got underway at 8 p.m. Thursday in Detroit and ends on Saturday.

The Jets have eight picks in the 2024 NFL Draft, including the final pick, aka "Mr. Irrelevant."

Joel Embiid has been experiencing Bell's palsy symptoms, he said after Philadelphia's 125-114 win over the New York Knicks.

A long-lost guitar that belonged to John Lennon has been found, and it will be on display and up for auction in New York City.

Drivers entering Manhattan below 60th Street will be hit with new tolls on June 30.

We're joined by the SoHo restaurant's Michelin-starred Chef Shaun Hergatt.

A group of pro-Israel demonstrators gathered outside Columbia University, where the student protesters' encampment remains in place. CBS New York's Christina Fan has the latest from campus.
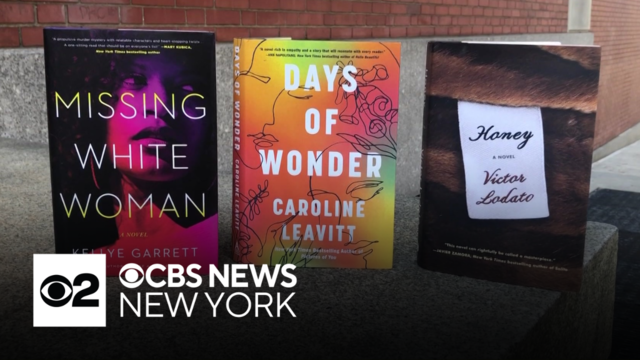
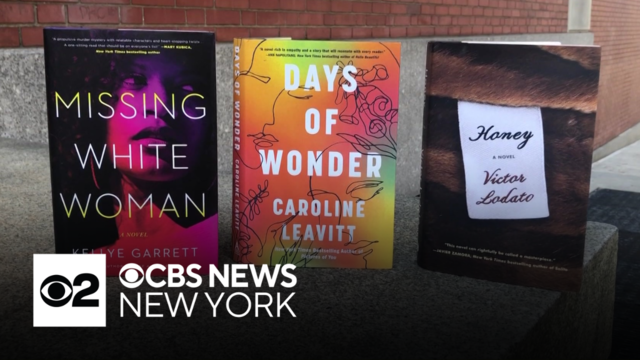
The CBS New York Book Club with Mary Calvi is voting on its next Fic Pick to read this month.

Reaction has been pouring in after the New York State Court of Appeals overturned the disgraced movie producer's 2020 rape conviction. CBS New York Elijah Westbrook has the latest details.

A great investigative news tip should explain the situation in detail, be newsworthy, and have real-world consequences.

New Yorkers still don't know what caused the deadly parking garage collapse in Lower Manhattan more than a year ago, but investigators just ruled out at least one possibility.
Many romance scam support groups are full of people making other questionable promises of recovering funds, the CBS New York Investigative Team found.

The DOJ is threatening to sue the NYPD if the practice of parking on sidewalks and crosswalks continues.

A New York City company promoted "$0 cost" COVID tests, then got over 100 complaints after people were told they may owe hundreds.

One year ago, a deadly New York City parking garage collapse sparked calls for increased oversight, but CBS New York has found inspections are past due for hundreds of garages across the city.

One person was killed and five others were injured in the parking garage collapse on Ann Street in the Financial District on April 18, 2023.

Three New York companies say their bills are being ignored after lighting up Citi Field for the Amaze Light Festival.

A new report from the NYPD's court-appointed monitor says the department still has plenty of work to do to address racial disparities in policing.

The MTA has revealed the start date of its controversial congestion pricing plan, which it says will result in 100,000 fewer vehicles in the "Congestion Relief Zone" every day.

New York City's Open Streets program is back for the 2024 season, which means regular street closures across the five boroughs.

One year ago, a deadly New York City parking garage collapse sparked calls for increased oversight, but CBS New York has found inspections are past due for hundreds of garages across the city.

Street vendors in the Bronx are calling on the city to fix the system for getting a vending license.

Some Queens residents are fuming over cars parking on beloved greenway.

The 12th Annual Black Comic Book Festival returns to the Schomburg Center later this week.

There are plans to turn an Inwood parking lot into new affordable apartments for the community.

From affordable housing to commercial properties, New York City developers are addressing the climate crisis in a variety of ways.

A New York City organization is taking action to clean up drug needles and syringes littering a South Bronx park.

Brooklyn Charter School in Bed-Stuy is trying to help parents with the cost of child care by expanding the school day to 12 hours.

Residents in Southern Brooklyn are concerned over MTA's proposed changes as part of the Brooklyn Bus Network Redesign.

Buzunesh Deba, who lives in the Bronx, became the default winner of the 2014 Boston Marathon in 2016 when the first-place winner was disqualified for doping, but she says she has not yet received her prize money.

Watch our special program, "Empire State Eclipse." CBS New York had a team of reporters spread across the state covering the rare total solar eclipse as the path of totality moved through the state.
Many people want to understand how to overcome loneliness. Loneliness can impact just about anyone of any age and any circumstance. You can feel lonely with friends or family, at your job, or in a crowd.
Long before we knew the names Uvalde, Pulse Nightclub, Parkland, and Sandy Hook, the nation was stunned and horrified by the Long Island Rail Road massacre.
David Schechter explores the connection between wildfires and climate change for "On The Dot."

Experts say climate change will continue to impact the Tri-State Area, driving bigger storm surges, more intense rainfall more often, and extreme heat that lingers longer, to name a few.
In 2021, 44% of high school students reported they persistently felt sad or hopeless, according to the Centers for Disease Control and Prevention. That's why CBS2 launched a series of special reports on breaking the stigma when it comes to children and mental health.

Superstorm Sandy was deadly, destructive and relentless. Ten years after Sandy, the hardest-hit areas are recovering and rebuilding.

CBS2 honors and celebrates the contributions of Black people to American history in our special.

From the top of a volcano in Hawaii to highways across the country, we'll help you understand where carbon dioxide in the atmosphere comes from and how it's warming our planet.
If you or someone you know needs help, you can call or text 988 to speak with a trained, caring counselor.

A non-profit called The JED Foundation is working with college campuses nationwide to help college students who may be struggling with their mental health. Dr. Michelle Mullen, senior vice president and chief design and impact officer at The JED Foundation joins CBS New York to discuss.

Your 20s are often referred to as the best time of your life, but for a lot of people, they can be a time of uncertainty at work in relationships and in regards to mental health. Dr. Meg Jay, an author and clinical psychologist, joins us to share her research.

Recent studies have found up to half of adolescents in the U.S. have engaged in self-harm at least once, often starting between the ages of 12 and 14. We're joined by psychologist Dr. Jennifer Hartstein, whose practice specializes in treating young people.

The technology gives users access to stress relief and relaxation techniques with practically the push of a button.

We hear from an expert who says boys often suffer in silence and shares advice for how parents can help.
Many people want to understand how to overcome loneliness. Loneliness can impact just about anyone of any age and any circumstance.

The forced isolation prompted increased feelings of despair and hopelessness. So how do we check in and support them four years later?

A recent study published in the journal JAMA Psychiatry suggests poor mental health may be a contributing factor.

The New York Jets used their 2024 NFL Draft first round draft pick on Penn State tackle Olumuyiwa "Olu" Fashanu.

The New York Giants selected wide receiver Malik Nabers with the 6th overall pick in the 2024 NFL draft.

Joel Embiid has been experiencing Bell's palsy symptoms, he said after Philadelphia's 125-114 win over the New York Knicks.

Defensemen Brent Burns and Dmitry Orlov got Carolina off to a fast start and the Hurricanes held on to beat the New York Islanders 3-2 on Thursday night for a 3-0 lead in the first-round series.

Joel Embiid scored 50 points, making all four 3-point attempts and scoring 18 in a potential series-shifting third quarter on Thursday night to lead the Philadelphia 76ers to a 125-114 win over the New York Knicks in Game 3 of their Eastern Conference first-round series.

Younger adults are aging faster, increasing their risk for early onset cancers. So which anti-aging techniques actually work?

There's no safe time to look directly at the 2024 solar eclipse in the New York City area because it's outside the path of totality. Dr. Nidhi Kumar explains why you need special eclipse glasses to prevent permanent eye damage.
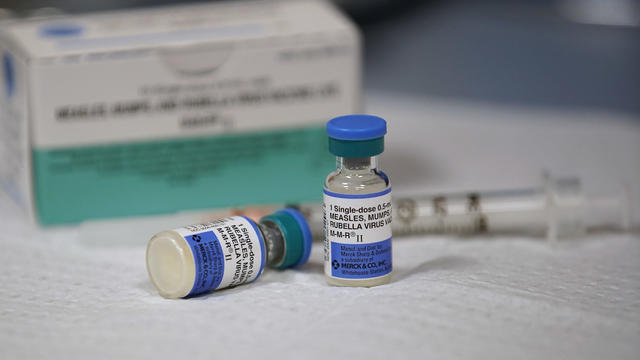
According to the CDC, cases of the highly infectious disease have already exceeded the total number of cases for all of 2023.

The CDC says roughly 25% of Americans suffer from season allergies, and studies suggest pollen season is getting longer and more intense.

Dr. Nidhi Kumar is On Call for CBS New York to break down the most common sleep disorders.
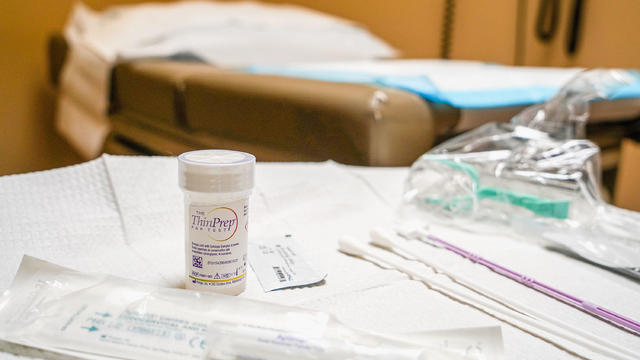
With expanded screening, treatment and vaccination, experts believe cervical cancer can be completely eliminated.

Maternal mortality continues to rise in the U.S., and a recent study suggests poor mental health may be a factor.

While very important, only 8% of patients attend the recommended 36 sessions of cardiac rehab.

Atrial fibrillation, or a-fib, is serious heart condition that causes abnormal heart rhythm.

More than 6 million Americans are living with dementia, and while there is no cure, patients can be helped by music.

Join CBS New York's Steve Overmyer in a tribute to winter in the Big Apple, when Christmas dreams and Hanukkah hopes brighten the skyline and warm our hearts even on the coldest nights.

Join us for a special Thanksgiving edition of stories of gratitude with CBS New York’s Steve Overmyer.

Get ready for a spine-chilling adventure as we delve into the world of the supernatural!

One man is making it his mission to give the heart of New York a heartbeat.
The CBS New York Book Club with Mary Calvi is voting on its next Fic Pick to read this month.

They discussed Pataki's book "Finding Margaret Fuller."
Will it be "Missing White Woman" by Kellye Garrett, "Days of Wonder" by Caroline Leavitt, or "Honey" by Victor Lodato?

It's time to vote on which book to read next: "Missing White Woman" by Kellye Garrett, "Days of Wonder" by Caroline Leavitt, or "Honey" by Victor Lodato.
Our book club with Mary Calvi has a bonus read that is hitting shelves and sites next week. Hear from the author, Ruth Reichl.

Meet freshman Luke Kugler and sophomore Gabriella Sherlock, who are dominating here at home and on the national level.

CBS New York's Chris Wragge spent the morning at the school that has everything from a fencing program to 3D printing.

Class Act with Chris Wragge heads to Long Island tomorrow for a live look at the school and its students.

CBS New York's Chris Wragge will be live from the high school this Friday morning.
CBS New York's Chris Wragge will be live at the Long Island high school this Friday morning.
This Friday, our morning show will be live from Oyster Bay High School in Nassau County.

CBS New York's Class Act with Chris Wragge is live this morning from the nearly-century-old school.

Arts High School of Newark has been around for nearly a century, and it's a school where dreams come true -- not for a few, but for many.

Be sure to join us Friday, when we'll be live all morning from Newark Arts High School.

For anyone living in New York City (or planning to move into Manhattan), and who's looking to save money by bundling their TV and home Internet service, here are the best options.

Need internet at your new home ASAP? Here's how to set up a simple, painless transfer that'll have you online in no time.

Before you make the big move to the Big Apple, make sure your new home internet is the fastest, and offers the best value.

The New York Jets used their 2024 NFL Draft first round draft pick on Penn State tackle Olumuyiwa "Olu" Fashanu.

The MTA has revealed the start date of its controversial congestion pricing plan, which it says will result in 100,000 fewer vehicles in the "Congestion Relief Zone" every day.

The New York Giants selected wide receiver Malik Nabers with the 6th overall pick in the 2024 NFL draft.

A long-lost guitar that belonged to John Lennon has been found, and it will be on display and up for auction in New York City.

Street vendors in the Bronx are calling on the city to fix the system for getting a vending license.

CBS New York's Vanessa Murdock looks back at historic tornado outbreaks, which highlight the fact that we don't have to be in the thick of severe weather season to witness a touchdown.
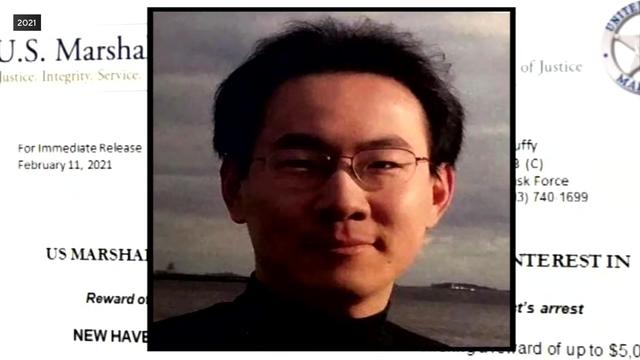
Former MIT researcher Qinxuan Pan has been sentenced to 35 years in prison in the 2021 murder of Yale graduate student Kevin Jiang.

Two heroic men saved a little girl that was running into into a busy intersection in East Hartford, Connecticut.

Expect to see a passing shower this afternoon, with a rumble here and there. Temperatures will be in the upper 60s to around 70 degrees.

U.S. News & World Report on Tuesday released their 2024 high school rankings, including nearly 2,000 in New York, New Jersey and Connecticut combined.

The New York Giants selected wide receiver Malik Nabers with the 6th overall pick in the 2024 NFL draft.

Newark Mayor Ras Baraka says the city will start enforcing its curfew for kids on May 3 after an uptick in crimes involving suspects under 18.

CBS New York's Vanessa Murdock looks back at historic tornado outbreaks, which highlight the fact that we don't have to be in the thick of severe weather season to witness a touchdown.

At least two Princeton University students were arrested Thursday at a pro-Palestinian protest on campus where students began setting up tents.

A New Jersey woman has received a first-of-its-kind transplant using a modified pig kidney along with a heart pump.

CBS New York's Vanessa Murdock looks back at historic tornado outbreaks, which highlight the fact that we don't have to be in the thick of severe weather season to witness a touchdown.

Twenty years after the remains of two Gilgo Beach victims were found in Manorville, a widespread search has resumed there.

Gov. Hochul secures funding for New Yorkers struggling with mental illness and involved in the criminal justice system.

Authorities with several law enforcement agencies continue to search an area in Manorville for evidence in the Gilgo Beach murders case.

U.S. News & World Report on Tuesday released their 2024 high school rankings, including nearly 2,000 in New York, New Jersey and Connecticut combined.

Former National Enquirer boss David Pecker appeared on the stand for the third day, detailing an agreement the tabloid made with a former Playboy model.

Former President Donald Trump visited a construction site in Midtown for an NYC rally before returning to court in his alleged "hush money" trial.

Gov. Hochul secures funding for New Yorkers struggling with mental illness and involved in the criminal justice system.
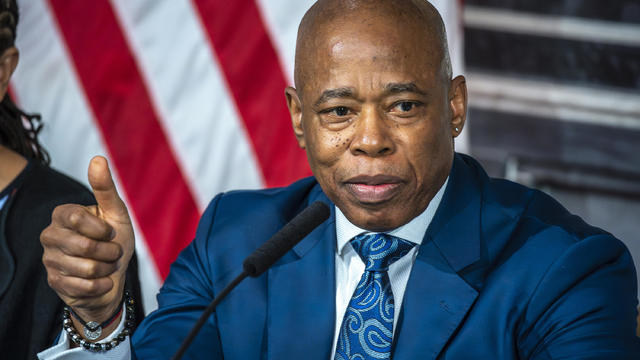
Mayor Eric Adams announced New York City's executive budget for the next fiscal year on Wednesday.

House Speaker Mike Johnson was met with loud boos as he visited Columbia University, where he joined calls for the president's resignation amid pro-Palestinian protests.

Joel Embiid has been experiencing Bell's palsy symptoms, he said after Philadelphia's 125-114 win over the New York Knicks.

A New Jersey woman has received a first-of-its-kind transplant using a modified pig kidney along with a heart pump.
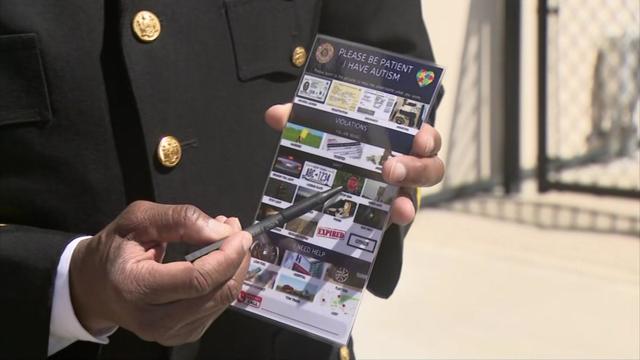
Suffolk County law enforcement officers are now equipped with a tool to help people on the autism spectrum during stressful encounters.

High blood pressure, or hypertension, may increase the risk of dementia, according to a new study. Hear from a doctor for advice on lowering your risk factors.

A New York City company promoted "$0 cost" COVID tests, then got over 100 complaints after people were told they may owe hundreds.

A long-lost guitar that belonged to John Lennon has been found, and it will be on display and up for auction in New York City.

Harvey Weinstein's 2020 conviction on felony sex crime charges has been overturned by the State of New York Court of Appeals.

Mary J. Blige, Cher, Foreigner, A Tribe Called Quest, Kool & The Gang, Ozzy Osbourne, Dave Matthews Band and Peter Frampton have been named to the Rock & Roll Hall of Fame.

The classic musical, which first opened in 1966, is back on Broadway in an immersive new production titled "Cabaret at the Kit Kat Club," starring Eddie Redmayne, Gayle Rankin and Bebe Neuwirth. Leave your troubles outside!

Taylor Swift's new album, "The Tortured Poets Department," was released Friday, and Swifties in New York City came together to celebrate.

The New York Jets used their 2024 NFL Draft first round draft pick on Penn State tackle Olumuyiwa "Olu" Fashanu.

The New York Giants selected wide receiver Malik Nabers with the 6th overall pick in the 2024 NFL draft.

Joel Embiid has been experiencing Bell's palsy symptoms, he said after Philadelphia's 125-114 win over the New York Knicks.

Defensemen Brent Burns and Dmitry Orlov got Carolina off to a fast start and the Hurricanes held on to beat the New York Islanders 3-2 on Thursday night for a 3-0 lead in the first-round series.

Joel Embiid scored 50 points, making all four 3-point attempts and scoring 18 in a potential series-shifting third quarter on Thursday night to lead the Philadelphia 76ers to a 125-114 win over the New York Knicks in Game 3 of their Eastern Conference first-round series.

Street vendors in the Bronx are calling on the city to fix the system for getting a vending license.

Some Queens residents are fuming over cars parking on beloved greenway.

The 12th Annual Black Comic Book Festival returns to the Schomburg Center later this week.

There are plans to turn an Inwood parking lot into new affordable apartments for the community.

From affordable housing to commercial properties, New York City developers are addressing the climate crisis in a variety of ways.

The Francis Scott Key Bridge in Baltimore collapsed early Tuesday, March 26 after a column was struck by a container ship that reportedly lost power, sending vehicles and people into the Patapsco River.

The 50th Annual Village Halloween Parade drew massive crowds, celebrating the theme "Upside/Down:Inside/OUT."

As much of the northeast experiences heavy rains, parts of New York City are beginning to flood.

Thousands of people flooded Union Square on Friday for a PlayStation giveaway promoted by livestreamer Kai Cenat.

A crane went up in flames high above Manhattan, then partially collapsed onto the street below.

Drivers entering Manhattan below 60th Street will be hit with new tolls on June 30.

We're joined by the SoHo restaurant's Michelin-starred Chef Shaun Hergatt.

A group of pro-Israel demonstrators gathered outside Columbia University, where the student protesters' encampment remains in place. CBS New York's Christina Fan has the latest from campus.
The CBS New York Book Club with Mary Calvi is voting on its next Fic Pick to read this month.

Reaction has been pouring in after the New York State Court of Appeals overturned the disgraced movie producer's 2020 rape conviction. CBS New York Elijah Westbrook has the latest details.